- Category Business
- Version3.454.0
- Downloads 1.00M
- Content Rating Everyone
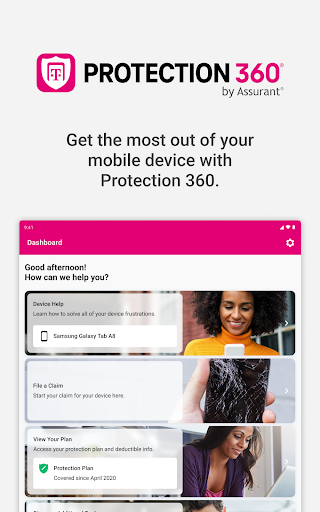
Protection 360™: Your Comprehensive Cybersecurity Companion for Modern Workflows
Protection 360™ is designed as an all-encompassing security solution that seamlessly integrates into business environments, safeguarding digital assets with a user-friendly approach.
Who's Behind the Shield?
Developed by CyberSecure Innovations, a team renowned for their expertise in cybersecurity solutions and enterprise software, Protection 360™ aims to provide robust yet accessible protection tailored for today's fast-paced, interconnected workplaces.
Bright Spots: What Makes Protection 360™ Stand Out
- Unified Threat Detection: Combines virus scanning, intrusion detection, and real-time monitoring into one streamlined platform.
- Collaborative Workflow Features: Facilitates secure, multi-user collaboration with built-in access controls and audit trails.
- Task and Incident Management: Offers integrated tools for tracking security incidents and managing response tasks efficiently.
- Adaptive Learning System: Utilizes machine learning to evolve defense mechanisms based on emerging threats.
A Burst of Security: The Engaging Introduction
Imagine waking up one morning to find your digital workspace under siege—files encrypted, unauthorized access detected—that's where Protection 360™ becomes your vigilant digital guardian. Unlike traditional security tools that sometimes act like digital bouncers, Protection 360™ feels like a dedicated security team working silently in the background, constantly watching for threats and making your workday smoother and safer. Its intuitive design transforms complex cybersecurity tasks into manageable, even engaging, activities—making security feel less like a chore and more like an active partner.
Core Functionality Deep Dive
1. Unified Threat Detection for Holistic Security
One of the standout features of Protection 360™ is its ability to bring together multiple security layers into a single dashboard. Think of it as a high-tech security command center, where everything from malware scans to network intrusion alerts populates one clear interface. Its real-time alerts ensure you're informed immediately if suspicious activity arises, greatly reducing reaction times. The platform's adaptive learning system enhances this further by analyzing your network's unique patterns, thereby tailoring defenses to your specific environment. This dynamic approach contrasts with many competing products that rely on static, signature-based methods—Protection 360™ learns, adapts, and evolves.
2. Collaborative Work Security – A Game Changer
While many security applications focus solely on individual devices or isolated network segments, Protection 360™ excels in safeguarding collaborative workflows. Its built-in collaboration tools enable teams to share sensitive data securely, with granular access controls that prevent unintended disclosures. The audit trail feature provides transparency, allowing managers to trace every action taken on key files and projects. This is especially valuable in environments where multiple stakeholders are working towards a common goal but need to maintain strict security protocols. Unlike traditional applications, which often treat security as an afterthought, Protection 360™ makes collaboration inherently secure, fostering trust and efficiency.
3. Task and Incident Management – Keeping the Security Frontline Organized
Dealing with security incidents can sometimes feel chaotic—imagine firefighting with no clear plan. Protection 360™ simplifies this with an integrated task management system that logs security issues, assigns response responsibilities, and tracks progress in real time. Whether it's patching vulnerability or conducting a breach investigation, teams have a centralized platform to coordinate actions, review historical data, and ensure nothing falls between the cracks. This systematic approach turns what could be a stressful emergency into a manageable, well-orchestrated process.
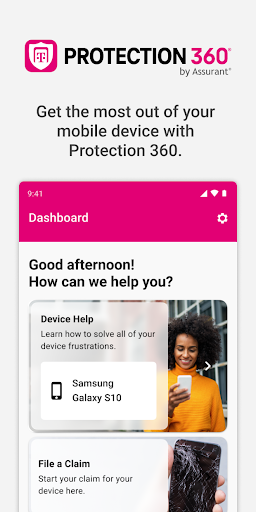
Ease of Use and User Experience
Protection 360™ boasts a clean, modern interface that resembles a sleek control panel—not unlike the cockpit of a well-designed aircraft. Navigation is intuitive; key features are accessible within a few clicks, and the layout minimizes clutter, allowing users to focus on what's important. The platform offers customizable dashboards, so security teams can prioritize the information most relevant to them. Importantly, the learning curve is gentle; even users with limited cybersecurity background find it straightforward to configure and operate. The responsiveness of the app is impressive—no delays or lag—ensuring that security teams can act swiftly without frustration.
Differentiating Factors: Standing Out in the Crowd
Compared to other business security tools, Protection 360™ puts a strong emphasis on collaborative security management, making it particularly suitable for teams that rely on seamless cooperation. Its integration of threat detection and response with task management enables a proactive cybersecurity posture—preventing threats before they become crises. Unlike traditional solutions that handle security as a series of isolated functions, Protection 360™ offers an interconnected ecosystem that emphasizes transparency and collective defense. This holistic approach makes it more adaptable and user-focused, especially in dynamic work environments where rapid decision-making is essential.
Final Verdict: Is It Worth It?
If you're seeking an intelligent, easy-to-use security platform that enhances collaborative work while providing comprehensive threat detection, Protection 360™ is definitely worth considering. It's particularly recommended for small to medium enterprises that value transparency, team coordination, and adaptive security measures. That said, larger organizations with complex infrastructures will also find its scalable architecture beneficial. For teams ready to elevate their cybersecurity game without drowning in technical complexity, this application offers a balanced combination of power, usability, and innovative features.
Pros
Comprehensive threat detection
Protection 360™ provides real-time scanning for viruses, malware, spyware, and phishing attempts, ensuring robust security.
User-friendly interface
The app offers an intuitive and simple interface suitable for users of all technical levels.
Multi-device protection
Supports safeguarding multiple devices simultaneously under a single account, ideal for families or small businesses.
Regular automatic updates
Ensures the app stays current with the latest security threats without manual intervention.
Additional privacy features
Includes features like VPN and anti-tracking tools to enhance user privacy online.
Cons
High battery consumption (impact: medium)
Protection 360™ may drain device battery faster during full system scans, which could affect usability.
Occasional false positives (impact: low)
Sometimes legitimate files are flagged as threats, but users can whitelist trusted files as a workaround.
Limited free features (impact: medium)
Many advanced features require a paid subscription; users can try basic protection for free before upgrading.
Initial setup complexity (impact: low)
New users may find configuring the app slightly confusing; official tutorials are recommended for guidance.
Performance impact on older devices (impact: medium)
On devices with limited RAM, the app may slow down system performance; closing background apps can help mitigate this.
You are going to be redirected to the official website to finish the download when you click the button above.
Frequently Asked Questions
How do I set up and start using Protection 360™ for the first time?
Download the app, register with your T-Mobile number, and follow the on-screen setup prompts to activate coverage and security features.
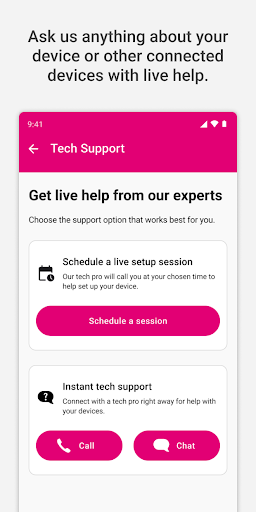
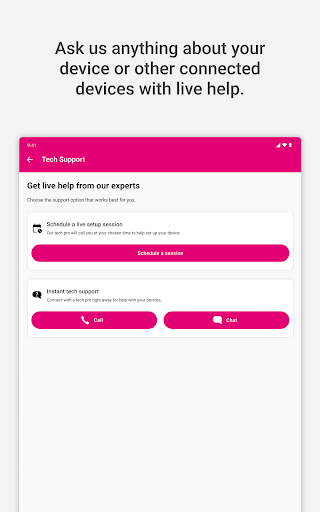
Can I access live tech support without extra charges?
Yes, live tech support is included for all Protection 360™ users and is available via call or chat, 7 days a week.
How do I file a claim for my damaged or lost device?
Open the app, navigate to 'Claim a Device,' and follow the simple steps to submit your repair or replacement request.
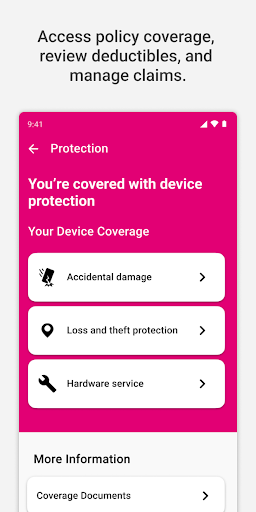
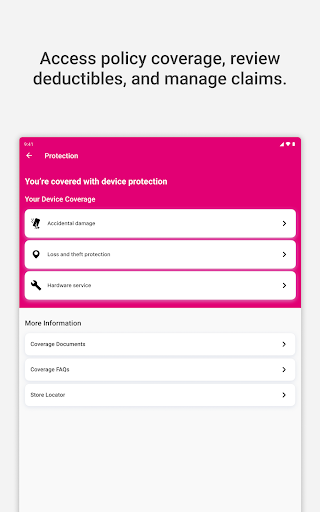
Where can I view my coverage details and FAQs?
Go to the 'Coverage' section within the app to see your coverage info, deductibles, and FAQs for better understanding.
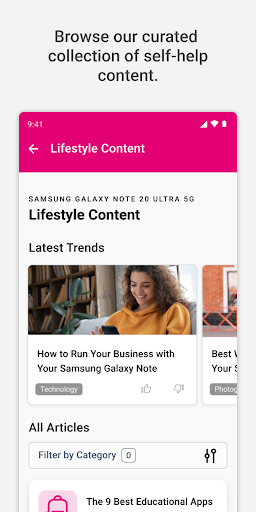
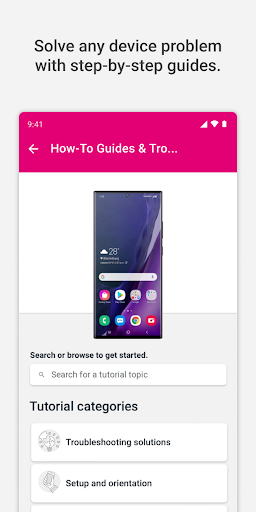
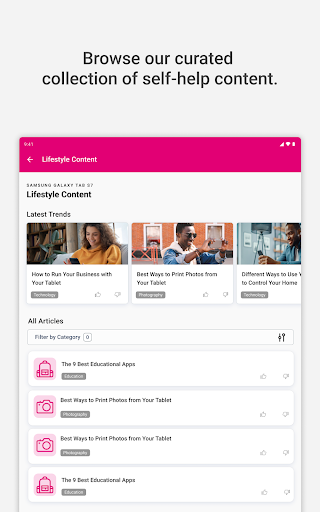
What self-help resources are available in the app?
Browse the curated articles and step-by-step guides in the 'Help' section to troubleshoot issues or optimize your device use.
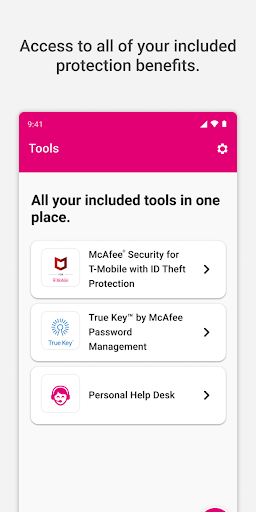
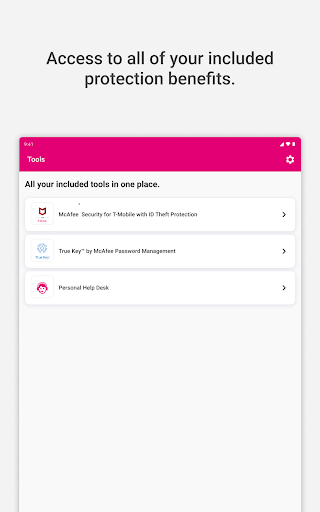
How can I manage or access my additional benefits?
Navigate to ‘Extras & Benefits' in the app to view and manage your available benefits by verifying your T-Mobile phone number.
Is there a cost for using Protection 360™ features like live support and claim filing?
No, these features are included at no extra charge for all Protection 360™ subscribers as part of your protection plan.
What should I do if I experience technical issues or the app isn't working properly?
Try restarting the app, checking your internet connection, or reinstalling. Contact support if problems persist via the app's help options.
Can I upgrade or change my coverage plan through the app?
Yes, you can view and modify your coverage plans by navigating to 'My Plan' in the app and following the instructions for upgrades.
Does Protection 360™ slow down my device or affect performance?
No, the app is lightweight and runs seamlessly in the background, ensuring your device's performance remains unaffected.






















